|
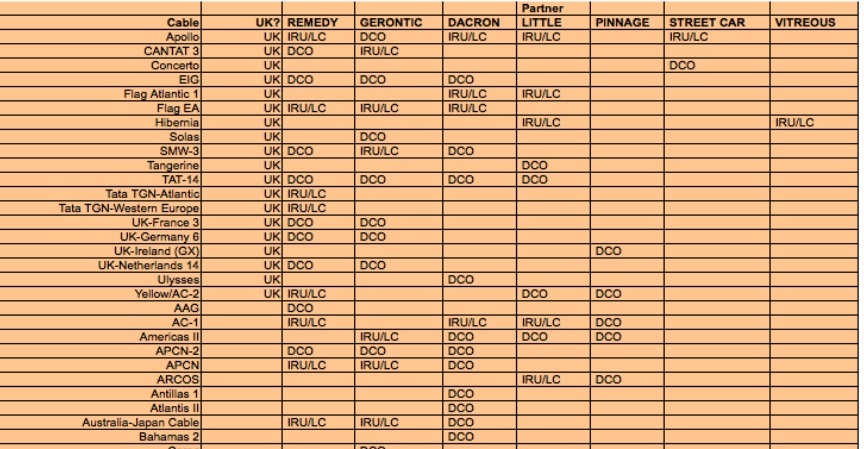
Documents reportedly from the Edward Snowden cache show that in 2009, GCHQ (and by association, the NSA) had access to the traffic on 63 submarine cable links around the globe. The cables listed handle the vast majority of international Internet traffic as well as private network connections between telecommunications providers and corporate data centers. According to a report in the German newspaper Süddeutsche Zeitung, the telecommunications company Cable & Wireless—now a subsidiary of Vodafone—“actively shaped and provided the most data to GCHQ surveillance programs and received millions of pounds in compensation.” The relationship was so extensive that a GCHQ employee was assigned to work full time at Cable & Wireless (referred to by the code name “Gerontic” in NSA documents) to manage cable-tap projects in February of 2009. By July of 2009, Cable & Wireless provided access to 29 out of the 63 cables on the list, accounting for nearly 70 percent of the data capacity available to surveillance programs. A Vodafone spokesperson did not deny the details when questioned by Süddeutsche Zeitung but said that any taps were performed legally under a warrant. Worldwide WebThe cable access wasn’t just used for surveillance—it was also used to pipe back data pulled from other networks through “computer network exploitation” (CNE) operations to populate Incenser, a GCHQ “special source collection system” running in a data center at GCHQ’s signals collection center at Bude in Cornwall. One of the networks that was targeted by a CNE hack and accessed over Cable & Wireless capacity, according to an NSA slide, was the Fiber-Optic Link Around the Globe (FLAG), a global network operated by the Indian telecommunications company Reliance Communications’ subsidiary, Global Cloud Xchange. Data pulled the FLAG network’s connections span the globe, with landing points in the US, Europe, North Africa, the Saudi Peninsula, India, Malaysia, China, Taiwan, South Korea, and Japan. The extent of the cable taps had been hinted at before in Snowden documents detailing Turbulence and Xkeyscore, the global distributed mass surveillance platform deployed by the NSA to search through the contents of Internet traffic. Taps into trans-oceanic cables were also revealed to be part of the NSA’s MUSCULAR program, which tapped into the private connections between the data centers of Yahoo and Google. But the latest documents reveal the actual names of the cables the NSA and GCHQ had access to as of 2009 as well as their “egress” speed—the volume of data that the agencies could pull from the cables. As of July of 2009, relationships with three telecom companies provided access to 592 10-gigabit-per-second pipes on the cables collectively and 69 10-gbps “egress” pipes through which data could be pulled back. The July 2009 documents included a shopping list for additional cable access—GCHQ sought to more than triple its reach, upping access to 1,693 10-gigabit connections and increasing egress capacity to 390. The documents revealed a much shorter list of “cables we do not currently have good access [to].” It’s not clear from the documents whether any of the 63 cable taps on the GCHQ list are NSA-provided, though a number of them have US landfalls—including Pacific cables connecting from the US to Japan and China and a number of cables serving the Caribbean, South, and Central America. http://arstechnica.com/tech-policy/2014/11/new-snowden-docs-gchqs-ties-to-telco-gave-spies-global-surveillance-reach/ Comments are closed.
|
Archives
March 2021
|
 RSS Feed
RSS Feed