|
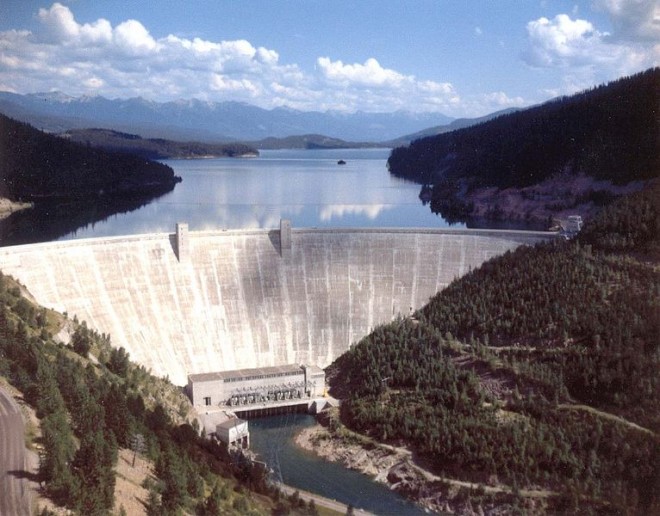
BY KIM ZETTER A hacker compromised a U.S. Army database that holds sensitive information about vulnerabilities in U.S. dams, according to a news report. The U.S. Army Corps of Engineers’ National Inventory of Dams contains information about 79,000 dams throughout the country and tracks such information as the number of estimated deaths that could occur if a specific dam failed. It’s accessible to government employees who have accounts. Non-government users can query the database but cannot download data from it. The breach began in January and was only uncovered in early April, according to the Free Beacon, a nonprofit online publication, which first published the news. Pete Pierce, a spokesman for the Army Corps of Engineers, did not return a call from Wired but confirmed to the Free Beacon that the breach occurred. “The U.S. Army Corps of Engineers is aware that access to the National Inventory of Dams (NID), to include sensitive fields of information not generally available to the public, was given to an unauthorized individual in January 2013 who was subsequently determined to not to have proper level of access for the information,” Pierce said in a statement to the publication. “[U.S. Army Corps of Engineers] immediately revoked this user’s access to the database upon learning that the individual was not, in fact, authorized full access to the NID.” The Corps of Engineers announced on its website that account usernames and passwords had since changed “to be compliant with recent security policy changes.” All users had been sent an e-mail notification to this effect, which apparently told them that their account username had been changed to their e-mail address and included the new password in plaintext that the Corps did not ask users to change. “When logging into the site with your new password for the first time, it is highly recommended that you copy/paste your password from the email you received rather than manually typing the password,” the notice on the website reads. Although the website provides links to reset the password if a user forgets it, the links were not working when Wired visited the site. Unnamed U.S. officials told the Free Beacon that the breach was traced to “the Chinese government or military cyber warriors,” but offered no information to support the claim. Hackers can use proxy servers or hijacked computers to conduct a breach and make it look as if the source was a specific country or individual. Michelle Van Cleave, a former senior adviser to the Executive Agent for Homeland Security and Department of Defense and a former consultant to the CIA, told the publication that the breach appeared to be part of an effort to collect “vulnerability and targeting data” for future cyber or military attacks, though she didn’t say how she came to this conclusion. “In the wrong hands, the Army Corps of Engineers’ database could be a cyber attack roadmap for a hostile state or terrorist group to disrupt power grids or target dams in this country,” she told the publication. http://www.wired.com/threatlevel/2013/05/hacker-breached-dam-database/ Editor's Note:
Here we go with the Dams, again. Comments are closed.
|
Archives
March 2021
|
 RSS Feed
RSS Feed